iptables firewall is used to manage packet filtering and NAT rules. IPTables comes with all Linux distributions. Understanding how to setup and configure iptables will help you manage your Linux firewall effectively.
iptables tool is used to manage the Linux firewall rules. At a first look, iptables might look complex (or even confusing). But, once you understand the basics of how iptables work and how it is structured, reading and writing iptables firewall rules will be easy.
This article is part of an ongoing iptables tutorial series. This is the 1st article in that series.
This article explains how iptables is structured, and explains the fundamentals about iptables tables, chains and rules.
On a high-level iptables might contain multiple tables. Tables might contain multiple chains. Chains can be built-in or user-defined. Chains might contain multiple rules. Rules are defined for the packets.
So, the structure is: iptables -> Tables -> Chains -> Rules. This is defined in the following diagram.
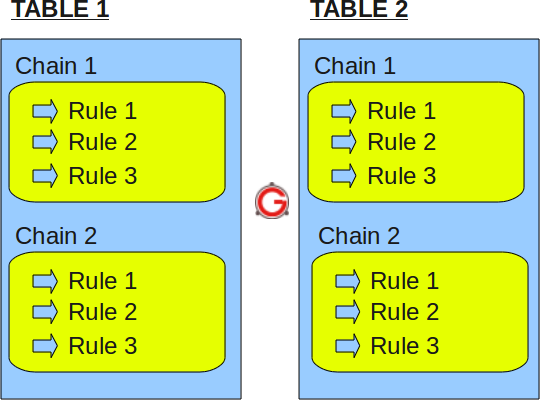
Fig: IPTables Table, Chain, and Rule Structure
Just to re-iterate, tables are bunch of chains, and chains are bunch of firewall rules.
I. IPTABLES TABLES and CHAINS
IPTables has the following 4 built-in tables.
1. Filter Table
Filter is default table for iptables. So, if you don’t define you own table, you’ll be using filter table. Iptables’s filter table has the following built-in chains.
- INPUT chain – Incoming to firewall. For packets coming to the local server.
- OUTPUT chain – Outgoing from firewall. For packets generated locally and going out of the local server.
- FORWARD chain – Packet for another NIC on the local server. For packets routed through the local server.
2. NAT table
Iptable’s NAT table has the following built-in chains.
- PREROUTING chain – Alters packets before routing. i.e Packet translation happens immediately after the packet comes to the system (and before routing). This helps to translate the destination ip address of the packets to something that matches the routing on the local server. This is used for DNAT (destination NAT).
- POSTROUTING chain – Alters packets after routing. i.e Packet translation happens when the packets are leaving the system. This helps to translate the source ip address of the packets to something that might match the routing on the desintation server. This is used for SNAT (source NAT).
- OUTPUT chain – NAT for locally generated packets on the firewall.
3. Mangle table
Iptables’s Mangle table is for specialized packet alteration. This alters QOS bits in the TCP header. Mangle table has the following built-in chains.
- PREROUTING chain
- OUTPUT chain
- FORWARD chain
- INPUT chain
- POSTROUTING chain
4. Raw table
Iptable’s Raw table is for configuration excemptions. Raw table has the following built-in chains.
- PREROUTING chain
- OUTPUT chain
The following diagram shows the three important tables in iptables.
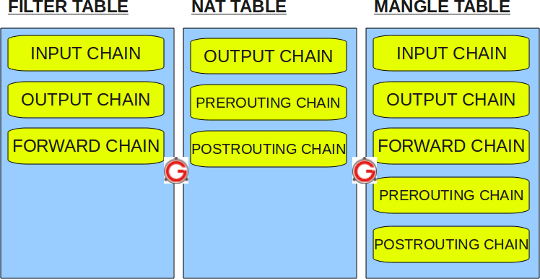
Fig: IPTables built-in tables
II. IPTABLES RULES
Following are the key points to remember for the iptables rules.
- Rules contain a criteria and a target.
- If the criteria is matched, it goes to the rules specified in the target (or) executes the special values mentioned in the target.
- If the criteria is not matached, it moves on to the next rule.
Target Values
Following are the possible special values that you can specify in the target.
- ACCEPT – Firewall will accept the packet.
- DROP – Firewall will drop the packet.
- QUEUE – Firewall will pass the packet to the userspace.
- RETURN – Firewall will stop executing the next set of rules in the current chain for this packet. The control will be returned to the calling chain.
If you do iptables –list (or) service iptables status, you’ll see all the available firewall rules on your system. The following iptable example shows that there are no firewall rules defined on this system. As you see, it displays the default input table, with the default input chain, forward chain, and output chain.
# iptables -t filter --list Chain INPUT (policy ACCEPT) target prot opt source destination Chain FORWARD (policy ACCEPT) target prot opt source destination Chain OUTPUT (policy ACCEPT) target prot opt source destination
Do the following to view the mangle table.
# iptables -t mangle --list
Do the following to view the nat table.
# iptables -t nat --list
Do the following to view the raw table.
# iptables -t raw --list
Note: If you don’t specify the -t option, it will display the default filter table. So, both of the following commands are the same.
# iptables -t filter --list (or) # iptables --list
The following iptable example shows that there are some rules defined in the input, forward, and output chain of the filter table.
# iptables --list Chain INPUT (policy ACCEPT) num target prot opt source destination 1 RH-Firewall-1-INPUT all -- 0.0.0.0/0 0.0.0.0/0 Chain FORWARD (policy ACCEPT) num target prot opt source destination 1 RH-Firewall-1-INPUT all -- 0.0.0.0/0 0.0.0.0/0 Chain OUTPUT (policy ACCEPT) num target prot opt source destination Chain RH-Firewall-1-INPUT (2 references) num target prot opt source destination 1 ACCEPT all -- 0.0.0.0/0 0.0.0.0/0 2 ACCEPT icmp -- 0.0.0.0/0 0.0.0.0/0 icmp type 255 3 ACCEPT esp -- 0.0.0.0/0 0.0.0.0/0 4 ACCEPT ah -- 0.0.0.0/0 0.0.0.0/0 5 ACCEPT udp -- 0.0.0.0/0 224.0.0.251 udp dpt:5353 6 ACCEPT udp -- 0.0.0.0/0 0.0.0.0/0 udp dpt:631 7 ACCEPT tcp -- 0.0.0.0/0 0.0.0.0/0 tcp dpt:631 8 ACCEPT all -- 0.0.0.0/0 0.0.0.0/0 state RELATED,ESTABLISHED 9 ACCEPT tcp -- 0.0.0.0/0 0.0.0.0/0 state NEW tcp dpt:22 10 REJECT all -- 0.0.0.0/0 0.0.0.0/0 reject-with icmp-host-prohibited
The rules in the iptables –list command output contains the following fields:
- num – Rule number within the particular chain
- target – Special target variable that we discussed above
- prot – Protocols. tcp, udp, icmp, etc.,
- opt – Special options for that specific rule.
- source – Source ip-address of the packet
- destination – Destination ip-address for the packet






 My name is Ramesh Natarajan. I will be posting instruction guides, how-to, troubleshooting tips and tricks on Linux, database, hardware, security and web. My focus is to write articles that will either teach you or help you resolve a problem. Read more about
My name is Ramesh Natarajan. I will be posting instruction guides, how-to, troubleshooting tips and tricks on Linux, database, hardware, security and web. My focus is to write articles that will either teach you or help you resolve a problem. Read more about
Comments on this entry are closed.
very good….keep writing……
Thanks
Pushpraj
Just note that DNAT and SNAT also stands for Dynamic and Static NAT, so don’t be confused when you read another text. Anyway, nice article, thanks!
Thank You Ramesh…very clear!
Excellent .. I was searching for a good article about the fundamentals of IPtable.. Thanks. Also waiting for next part
Nice article, look forward to rest of the series. Any idea when others will be out?
Some of your articles are excellent for beginners but this is not a tutorial it is misnamed.
This website is sooooo what I just need at work. Good work Ramesh, you’re a genuis.
Thanks a lot
Great topic. Looking forward to the rest of the series.
Ramesh,
You might want to include tutorial on fwbuilder, its a nice gui interface and used to manage firewall on 100’s of hosts.
-R
great stuff. also waiting for the follow up!
great read and informative. look forward to the follow up.
very helpfullllllll,,,
wait, for your next part.
Good tutorial, I find iptables complex to understand but you have made it so easy, Thanks.
Very Nice tutorial. Thanks
great starter to the series
plz continue with the tutorial
Nice job.I read it and got the concept where is confused.. i have some question and answers ,,u will help me out to be correct.
Q1: Rule the matches ssh traffic(tcp,22) arriving through interface eth0.
ans. iptables -A INPUT -i eth0 -p tcp –dport 22
OR
iptables -A INPUT -i eth0 -p tcp –sport 22
Q2: Rule that matches traffic to a DNS server (udp,53) from any address in the range 10.0.0.0-10.0.0.255
Ans: iptable -A INPUT -m iprange –src-range 10.0.0.0-10.0.0.255 -d 10.19.6.142 (dns server) -p udp –dport 53
Q3:Rule that matches traffic from any address in the range 10.0.0.1 to 10.0.0.6,inclusive.
Ans. iptable -A INPUT -m iprange –src-range 10.0.0.1-10.0.0.6
Q4: Three rules that accept traffic from address 10.0.0.1 through 10.0.0.6, but drops traffic from 10.0.0.0 and 10.0.0.7 , without using any extension matches.
Ans: iptable -A INPUT -s 10.0.0.0 -j DROP
iptable -A INPUT -s 10.0.0.7 -j DROP
iptable -A INPUT -m iprange –src-range 10.0.0.1-10.0.0.6 -j ACCEPT
thanks for the correct and replying
Now only I understand the firewall concepts and the Iptable rules…
Each and every technique of explaining the theories are brilliant Mr.Ramesh… Keep it up.. We all Are with YOU…
l think am beginning to understand the iptables, thanks man
how to define the rules’ prior then?
Ramesh,
Very good article. Thanks. Has anyone considered the pros/cons to utilizing and maintaining their own open source firewall vs. paying for the service (ie. Verizon, AT&T, other)? How much time is associated to maintaining/supporting an open source solution? I’m trying to justify the idea of going away from a service based concept (appliance, maintenance/support are provided) vs. pulling in my own skilled resources to build/maintain an open source solution as discussed above.
Thanks,
Rob
you said: “Iptables’s Mangle table is for specialized packet alteration. This alters QOS bits in the TCP header. ”
Alters QOS bits in TCP header? I thought mangle altering TOS bits in IP header! TCP operate on higher level than IP, and mangle works with IP packets.
it’s very nice thanks for your posting .keep writing about iptables
it was really good,thank u so much,plz keep writing…
Thanks, nice and clear
Really good and very clear ….
Nice post.Very helpful for beginners.
looking for a rule that allows traffic comming from an external user through the internet to access FTP (192.168.0.252), SSH& web (192.168.0.253) servers and some workstation on the same network. The router of that network is 192.168.254
Extraordinary introduction, Ramesh
You’ve the knowledge and astonishing skills to communicate it, an unusual combination
Congratulations!
LJ
Super..
Thanks for the article. Now I really understand how this stuff work. Awesome
Thank you very much for your excellent tutorial. Looking forward to the next one.
Regards to you !
thanks for your so popular article.
Thanks a lot. It really has been benificial in clearing out some concepts. By coincidence i came over to the 2nd article first and landed up over here otherwise would have been difficult.
Is there any directory structure where one can have overview of the topics. That would be helpful as well. (The reason being that your explanations are really from grass root level)
Regards
great article
Thank you for your article, It’s very good. 🙂
Great and thank you 😀
Thank you very much brother
Reall!!! nice and useful article for system admin’s
Great ant thank you
good iptables structured and all administrator can easily understand this.
Very NIce Article… 🙂
please add link for next page of current topic
Absolute BEAUTIFUL article. Very clear. For shame ALL the other posts out there including MAN pages.
A tear to my eye the series never continued….
Hi Ramesh Natarajan,
Thank you very much for your post. Earlier the concept of ‘iptables’ was like a nightmare and too complicated and overwhelming to understand. Thank you very much for making the concept so simple. The clear and precise explanation should be appreciated.
Extremely well explained, as concepts were organized properly and follow a logical progression. Most other articles I read never actually explained the definition of a “chain”!….. This article did a marvelous job.
Thanks Ramesh for simplyfying an abstract topic and explain it in such simple terms. Surely you have a knack to break down complex stuff into simple sentences. Thanks
Maryann
How to direct incoming traffic from a trusted network to a chain?
-A FORWARD -i eth1 -o trusted-outside -j ACCEPT
Many thanks Ramesh…
Very clean and elegant words! Wheres the next blog?
Nice article. and please update mangle rules.
This article is great and mentions that it is part of a series. Did any other parts get published?
excellent article for beginners like us !! taking this as the reference for preparing in lab exam.. thank you so much this great work.
from,
MTech Cyber Security (SNGCE)
thanks bro.
!!!!!!Great article!!!!!
Great explanation! Thanks!
Hi Ramesh,
Nice doc.
“Once the rule is not not matching then the packet is passed to the next rule.” – does it mean that it is passed to the next rule in the Sl. no ? Does these rules have any precedence kind of concept or the Sl.No of that rule signifies its precedence?
Continuation to my earlier question, once i configure three rules under INPUT chain of Filter Table, I do not see any sequence. If no sequence is maintained, then how the rule precedence works?
[root@mobst480m-lnx1 ~]# iptables –list
Chain INPUT (policy ACCEPT)
target prot opt source destination
DROP all — mobst480p-lnx1.englab.juniper.net anywhere
DROP all — cfdvipers-lnx2.englab.juniper.net anywhere
DROP all — mobst480o-lnx1.englab.juniper.net anywhere
Chain FORWARD (policy ACCEPT)
target prot opt source destination
Chain OUTPUT (policy ACCEPT)
target prot opt source destination
thanks ramesh. very helpful article 🙂
One thing though: it’s “one criterion”, not one “criteria”. Criteria is the plural (like “phenomena”)
Nice info on iptables. One thing worth mentioning is that iptables need be saved for them to stay intact after reboot.
why do we have same chains in diffrent tables of “iptables firewall”?
“So, if you don’t define you own table, you’ll be using filter…”
“You” should be “your”.
Just FYI.
Really Good. I learned a lot.
You are the best Linux geek who is able to explain simply such a complicated topic as Linux.
Nice article for beginners. But IMHO the final section with “iptables –list” output could use additional explanation.
What’s a Chain?
Coming from a network engineering background dealing with Cisco, Juniper, and Checkpoint firewalls, this is a perfect jumping off point for Linux host based FW. Sigh, why didn’t I find this before I spent money on a book that is now literally a paper weight.
I am using this box as Router and as per your suggestion in trial message I had configured the FORWARD chain of three user mac address, configuration mentioned below.
two User getting the IP Address from DHCP Server but not able to browser, so please can you help me how they can browse…..
DHCPACK on 192.168.23.171 to 90:72:40:58:a9:95 (is-iPhone)
DHCPACK on 192.168.23.178 to FC:75:16:67:3F:BE (android-f50ef57524010a1e)
DHCPACK on 192.168.23.100 to 00:25:64:A4:3F:01 (android-7306f0c1f5e73255)
# Generated by iptables-save v1.4.7
*filter
:INPUT ACCEPT [37:6239]
:FORWARD DROP [789:129680]
:OUTPUT ACCEPT [89:13144]
-A INPUT -i eth1 -m mac –mac-source 34:E67:00:B1:E6 -j ACCEPT
-A INPUT -s IP ADDRESS -p tcp -m tcp –dport 8888 -j ACCEPT
-A INPUT -s IP ADDRESS -p tcp -m tcp –dport 8888 -j ACCEPT
-A INPUT -s IP ADDRESS -p tcp -m tcp –dport 9888 -j ACCEPT
-A INPUT -s IP ADDRESS -p tcp -m tcp –dport 9888 -j ACCEPT
-A INPUT -p tcp -m tcp –dport 22 -j DROP
-A INPUT -p icmp -m icmp –icmp-type 8 -j DROP
-A INPUT -p tcp -m state –state NEW -m tcp –dport 80 -j ACCEPT
-A INPUT -p tcp -m state –state NEW -m tcp –dport 443 -j ACCEPT
-A FORWARD -i eth1 -j ACCEPT
-A FORWARD -m mac –mac-source FC:75:16:67:3F:BE -j ACCEPT
-A FORWARD -m mac –mac-source 00:25:64:A4:3F:01 -j ACCEPT
-A FORWARD -m mac –mac-source 90:72:40:58:A9:95 -j ACCEPT
-A OUTPUT -p icmp -m icmp –icmp-type 0 -j DROP
COMMIT
# Completed on Tue Jan 5 18:47:41 2016
# Generated by iptables-save v1.4.7 on Tue Jan 5 18:47:41 2016
*nat
:PREROUTING ACCEPT [406:28986]
:POSTROUTING ACCEPT [0:0]
:OUTPUT ACCEPT [1:108]
-A POSTROUTING -o eth0 -j MASQUERADE
COMMIT
# Completed on Tue Jan 5 18:47:41 2016
# Generated by iptables-save v1.4.7 on Tue Jan 5 18:47:41 2016
*mangle
:PREROUTING ACCEPT [1596:188447]
:INPUT ACCEPT [130:13127]
:FORWARD ACCEPT [1466:175320]
:OUTPUT ACCEPT [90:13236]
:POSTROUTING ACCEPT [767:58876]
COMMIT
# Completed
Really great 🙂
Thanks, Ramesh.
thank you very much
A very useful article
I am novice to this linux firewall.
I have now learn to configure the iptables & ip6tables
Very well explained!
good!
I have to redirect only the specific traffic to another port and drop the rest of it. How do I achieve this? The packet will be accepted first or pre-routing is done first?
nice article for the freshers to understand abt iptables….
thank you….
can anyone explain me line by line what these mean?:
this was created by an expert to allow ssh connection via an alternative internet line using a router which is behind that line on a separate LAN but having the LAN IP of the target line 10.0.0.37 (router’s WAN IP is 192.168.x.x -because it is inside a LAN of the other network)
This is very helpful, Thank you.